在渗透测试中使用fuzz技术
背景
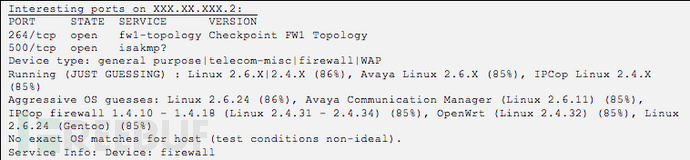
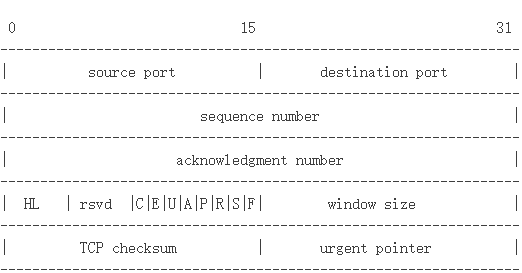
协议分析
工具选择
#!/usr/bin/env python # Fuzzing the initial 4-byte packet from client to CheckPoint VPN server. import time import sys from sulley import * # Time to wait between mutations SLEEP_TIME=0.5 # Time to wait before claiming a host is unresponsive TIMEOUT=3 # number of crashes to observe before skipping the remainder of a group CRASH_THRESHOLD=3 # Initialize the Sulley mutation descriptor s_initialize("SecuRemote-Initial-Packet") s_byte("\x51",full_range=True) s_static("\x00\x00\x00") print "Total mutations: " + str(s_num_mutations()) + "\n" print "Minimum time for execution: " + str(round(((s_num_mutations() * (SLEEP_TIME))/3600),2)) + " hours." print "Press CTRL/C to cancel in ", for i in range(5): print str(5 - i) + " ", sys.stdout.flush() time.sleep(1) # For debugging purposes, uncomment these lines to see Sulley's mutations # in hex dump format #print "Hex dump mutation output:" #while s_mutate(): # print s_hex_dump(s_render()) sess = sessions.session(session_filename="SecuRemote-Initial-Packet.sess", sleep_time=SLEEP_TIME, timeout=TIMEOUT, crash_threshold=CRASH_THRESHOLD) # Tie this session to the SecuRemote-Simple-String fuzzing cases sess.connect(s_get("SecuRemote-Initial-Packet")) # Change this IP address to the target system target = sessions.target("127.0.0.1", 264) # Add the target to the session (can be repeated for multiple targets) sess.add_target(target) # Kick off the fuzzer, monitoring with WebUI on localhost:26000 sess.fuzz()对有状态的协议进行测试
#!/usr/bin/env python from sulley import * SLEEP_TIME=0.5TIMEOUT=3CRASH_THRESHOLD=3# The function Sulley will run prior to sending each mutation. We leverage # it to setup the target system with the initial packets and response in the # protocol exchange prior to our target packet. def preconn(sock): sock.send("\x51\x00\x00\x00") time.sleep(0.5) sock.send("\x00\x00\x00\x21") # Set a socket timeout on the recv so we aren't waiting indefinitely if # the server crashed from a previous test case. sock.settimeout(5) response = sock.recv(4) print "Setup response: ", for i in response: print "%02x" % ord(i), print s_initialize("SecuRemote-Simple-String") # Create a size field, which is based on the content of the named block # Sulley uses ">" to indicate big-endian values, "<" is little-endian s_size("client-name-string", length=4, endian=">") # This is the block of data used for filling in the s_sizeif s_block_start("client-name-string"): # "securemote" is the default string s_string("securemote") # constant null terminator s_byte("\x00") s_block_end() sess = sessions.session(session_filename="Securemote-Simple-string.sess", sleep_time=SLEEP_TIME, timeout=TIMEOUT, crash_threshold=CRASH_THRESHOLD) # Call preconn() before each mutation is sent to setup the target sess.pre_send = preconn sess.connect(s_get("SecuRemote-Simple-String")) target = sessions.target("127.0.0.1", 264) sess.add_target(target) sess.fuzz()成果
相关文章
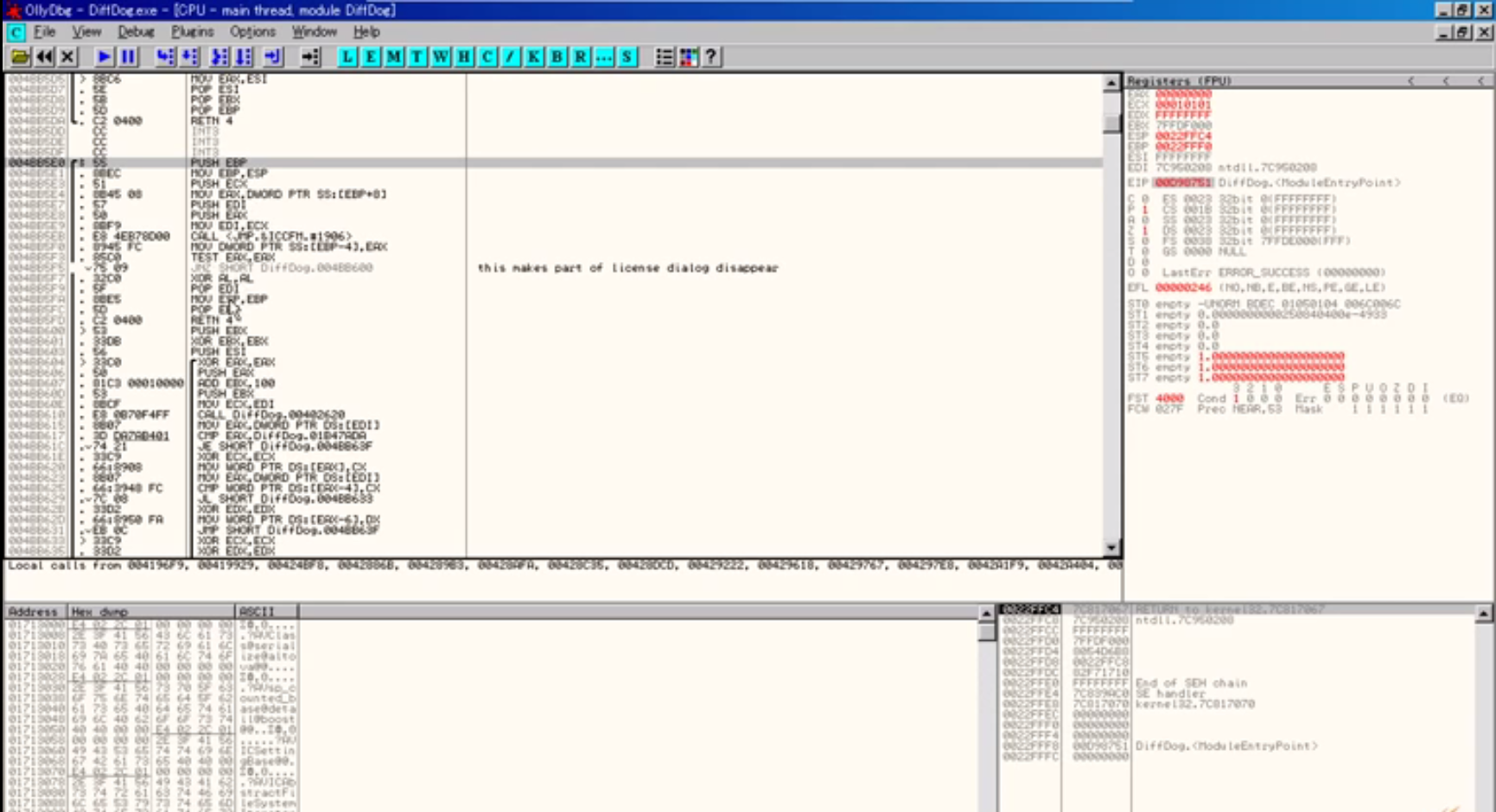
OllyDbg是不是适用全部电脑操作系统?
什么叫OllyDbg? 这一黑客工具是一个32位系统汇编器剖析程序调试。二进制代码剖析促使该专用工具在源不能用的状况下很有效。OllyDbg具备优良的操作界面,循环系统,API启用,高級编码剖析,可...
Stunnel应用OpenSSL库开展数据加密
什么叫Stunnel? 此专用工具致力于做为虚拟服务器和远程控制手机客户端中间的SSL数据加密包裝。要是工程建筑全过程合乎其安全设置,Stunnel能够从FIPS 140-2认证OpenSSL FI...
Argus是啥?
Argus是啥? Argus可用以协助适用网络信息安全管理方法和互联网调查取证。根据恰当的对策,克罗地亚数据信息能够 被采掘,以明确您是不是古代历史遭受侵入或进攻,在公布进攻并明确了让步指标值(IO...
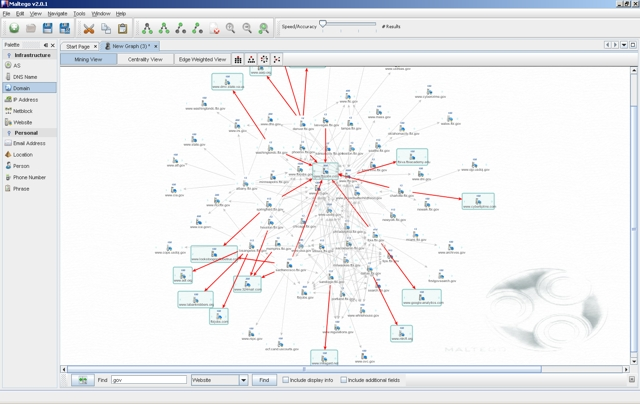
Maltego的典型性主要用途是啥?
什么叫Maltego? Maltego由Paterva开发设计,是用以开源系统调查取证和智能化的专用工具。其重中之重是出示一个变换库,用以发觉来源于不一样开源系统的数据信息,并将该大数据可视化为适用...
五招查出想要知道的IP地址
与好友在网络上相互传输资料时,有时先要知道对方计算机的IP地址,才能与对方建立信息传输通道。 那么对方的IP地址该如何搜查得到呢?这样的问题你也许会嗤之以鼻,的确,查询对方计算机的IP地址,实在简单...
tcpdumpthetrafficonanetwo
介绍: tcpdump全名:dump the traffic on a network,依据使用人的界定对互联网上的数据文件开展捕获的包分析工具。 tcpdump能够将互联网中传输的数据文件的“头”...


 免责声明:本站所发布的任何网站,全部来源于互联网,版权争议与本站无关。仅供技术交流,如有侵权或不合适,请联系本人进行删除。不允许做任何非法用途!
免责声明:本站所发布的任何网站,全部来源于互联网,版权争议与本站无关。仅供技术交流,如有侵权或不合适,请联系本人进行删除。不允许做任何非法用途!